Cracking the Code: How Hackers Use HACCP to Compromise Food Safety)
Cracking the Code: How Hackers Use HACCP to Compromise Food Safety)
The food industry is no stranger to the threat of cyberattacks. With the increasing reliance on technology and data connectivity, companies are vulnerable to a range of cyber threats. One of the most significant risks is the exploitation of Hazard Analysis and Critical Control Points (HACCP) systems, a critical tool in ensuring food safety.
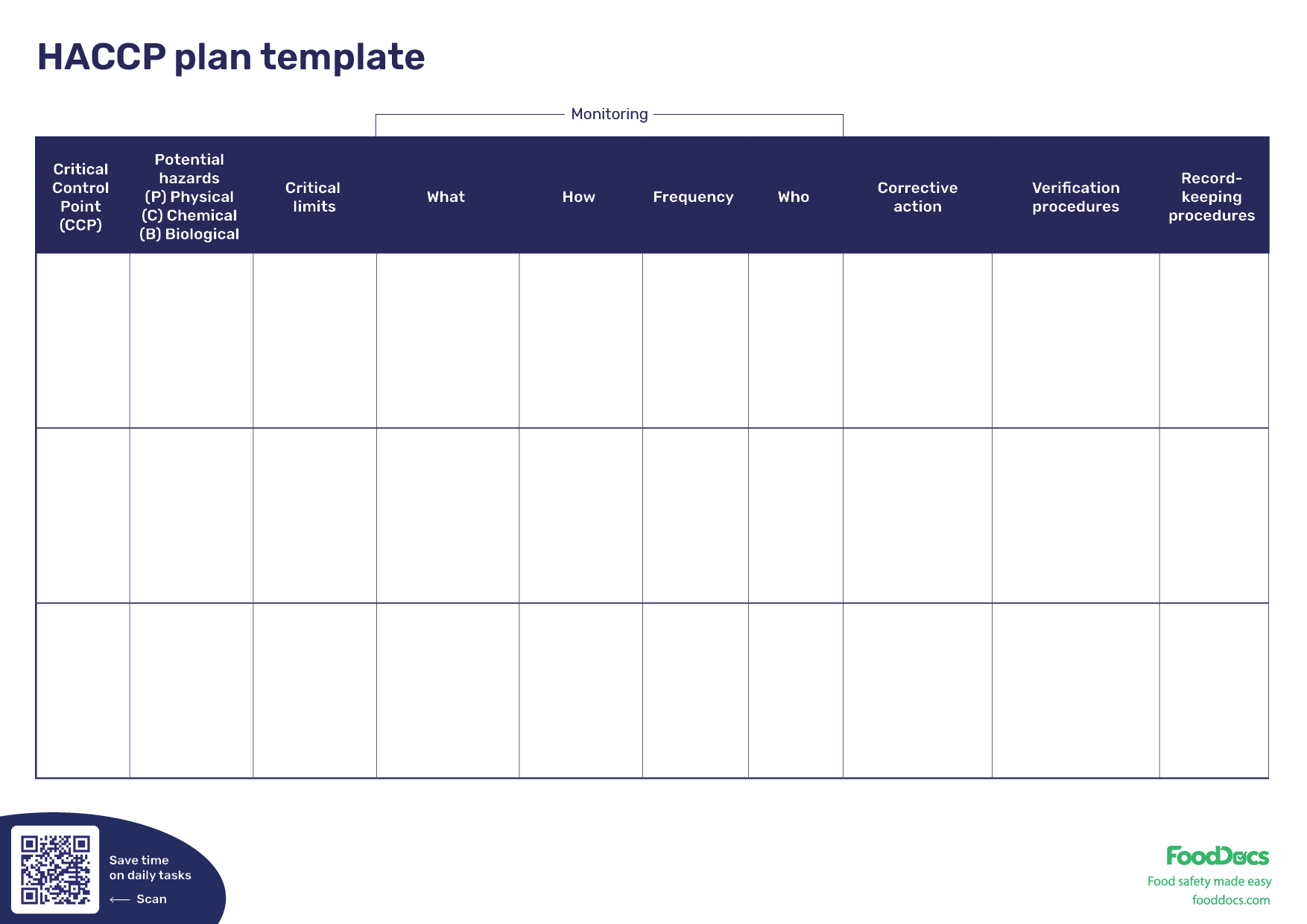
HACCP is a systematic approach to identifying and controlling hazards in the food production process. It involves identifying potential hazards, evaluating their severity and likelihood, and implementing controls to mitigate risks. However, when hackers target HACCP systems, they can compromise the integrity of the food supply chain, putting consumers at risk of foodborne illnesses. In this article, we will explore how hackers use HACCP to compromise food safety and the implications of these attacks.
The use of hacking to compromise food safety through HACCP is a growing concern. According to a report by the International Association of Crosby, nearly 50% of companies in the food and beverage industry have experienced a cyberattack. The cost of these attacks can be significant, with losses attributed to downtime, lost revenue, and damage to a company's reputation.
One of the most significant vulnerabilities in HACCP systems is the reliance on manual entry and data entry. When critical data is not properly validated, it can lead to errors and omissions that can compromise food safety. "The biggest challenge we face is trying to keep up with the volume of data that's coming in," said Karen Hickman, a food safety expert with over 20 years of experience. "If a hacker can get into the system and alter that data, it can have a significant impact on the safety of the food."
Hackers often target HACCP systems by exploiting vulnerabilities in the software or hardware used to implement the system. This can include using phishing scams to gain access to sensitive information or exploiting weaknesses in the network to gain unauthorized access. Once a hacker has accessed the system, they can alter critical data, insert malicious code, or even take control of the system.
Another significant vulnerability in HACCP systems is the lack of real-time monitoring and response. HACCP systems are often designed to monitor processes offline, with data entered manually or through automated systems. However, when a hacker has access to the system, they can suppress or alter data in real-time, making it difficult to detect any anomalies. "We need to be able to detect when something's going wrong in real-time," said Dr. Alina Teodor, a food safety expert at the University of California, Davis. "If we're not monitoring in real-time, we can miss critical information that could impact food safety."
The consequences of hacking HACCP systems can be severe. In 2019, a cyberattack on a Goya Foods plant in New Jersey resulted in the recall of over 3 million pounds of canned beans. The attack compromised the company's ability to track and respond to quality issues, putting consumers at risk of foodborne illness.
The impact of hacking HACCP systems can also be seen in the almost $50 billion in economic losses attributed to food recalls between 2013 and 2016.
To mitigate the risks associated with hacking HACCP systems, companies need to take a proactive approach to cybersecurity. This includes implementing robust firewalls and encryption, regularly updating software, and investing in advanced threat detection tools.
Companies also need to invest in training and education for their staff. This includes teaching employees about the risks associated with hacking and how to identify potential threats. According to a report by MySecurityMarket, 70% of companies that have experienced a cyberattack list inadequate employee training as a contributing factor.
In addition, companies need to prioritize robust data validation and verification procedures, ensuring that critical data is accurate and reliable. This includes implementing automated data validation and verification tools, as well as regular audits and testing of the system.
Finally, companies need to be prepared for the worst-case scenario. This includes having a comprehensive incident response plan in place, including procedures for notification and communication with regulatory bodies and law enforcement.
In conclusion, the use of hacking to compromise food safety through HACCP systems is a growing concern. Companies need to take a proactive approach to cybersecurity, investing in training, education, and technology to mitigate the risks associated with hacking HACCP systems. By taking these steps, companies can help ensure the integrity of the food supply chain and protect consumers from the risks associated with hacking HACCP systems.
The Importance of HACCP in Modern Food Production
With the increasing demand for food safety and quality, HACCP has become a critical component in modern food production. By identifying and controlling hazards, HACCP enables companies to produce safe and high-quality food products. However, when hackers target HACCP systems, they can compromise the integrity of the food supply chain, putting consumers at risk of foodborne illnesses.
Benefits of HACCP Implementation
Implementing HACCP can provide companies with several benefits, including
- Improved food safety
- Increased consumer confidence
- Reduced regulatory issues
- Improved food quality
- Reduced costs associated with product recalls
Common Vulnerabilities in HACCP Systems
There are several common vulnerabilities in HACCP systems that hackers can exploit to compromise food safety:
- Manual entry and data entry errors
- Weaknesses in software or hardware
- Lack of real-time monitoring and response
- Insufficient employee training and education
Best Practices for Mitigating Hacking Risks
To mitigate the risks associated with hacking HACCP systems, companies can implement the following best practices:
- Implement robust firewalls and encryption
- Regularly update software and hardware
- Invest in advanced threat detection tools
- Provide training and education for employees
- Implement automated data validation and verification procedures
- Have a comprehensive incident response plan in place
Conclusion
The use of hacking to compromise food safety through HACCP systems is a growing concern. Companies need to take a proactive approach to cybersecurity, investing in training, education, and technology to mitigate the risks associated with hacking HACCP systems. By implementing HACCP and following best practices for mitigating hacking risks, companies can help ensure the integrity of the food supply chain and protect consumers from the risks associated with hacking HACCP systems.



Related Post

The Elusive Middle Class: Navigating the Aspirations vs. Reality of Upward Mobility

The Ultimate Guide to Navigating Indeed.com for Job Seekers

<strong>Unlocking Freedom: The Power of Gtl Getting Out of Incarceration</strong>

Unlocking the Secrets of the 13 November Sun Sign: A Comprehensive Guide to the Scorpio-Taurus Cusp

