What Adversaries Look For When Gathering Intelligence: The Unseen Threats in the Digital Age
What Adversaries Look For When Gathering Intelligence: The Unseen Threats in the Digital Age
As the world becomes increasingly interconnected, the threat of cyberattacks and intelligence gathering by adversaries has never been more pronounced. In today's digital age, the ability to gather and analyze vast amounts of data has become a powerful tool for nation-states, terrorists, and other malicious actors to gain an upper hand. But what do these adversaries look for when gathering intelligence, and how can we mitigate these risks to protect our national security and individual privacy?
When it comes to gathering intelligence, adversaries often focus on acquiring sensitive information about individuals, organizations, and governments. This information can take many forms, including personal identifiable information (PII), financial data, and strategic security clearances. By gaining insight into these areas, adversaries can create targeted campaigns to compromise individual security, steal sensitive information, and disrupt critical infrastructure.
The Anatomy of an Intelligence Gathering Operation

An intelligence gathering operation typically begins with open-source intelligence (OSINT) collection. This involves scouring publicly available sources of information, such as social media, online forums, and government databases, to identify potential targets and gather initial intelligence. Once a target has been identified, the adversary will often shift to more advanced methods, such as phishing or spear phishing campaigns, to acquire sensitive information or gain access to secure systems.
According to a former NSA cyber intelligence official, "Many adversaries start with social media. They use it to gather information about individuals, organizations, and governments. They use this information to create targeted phishing campaigns, which can lead to significant compromises of sensitive information."
The Art of Social Engineering
Social engineering, the art of manipulating individuals into divulging sensitive information or gaining access to secure systems, is a particularly effective tactic for adversaries. This can take many forms, including:
*
Phishing campaigns, which involve sending targeted emails or messages with links or attachments to trick individuals into divulging sensitive information.
Spear phishing campaigns, which involve sending highly targeted emails or messages that appear to come from a trusted source, with the aim of gaining access to sensitive information or secure systems.
Whaling, a type of spear phishing that targets high-level executives or other key individuals with sensitive information or access.
According to the Ponemon Institute, 76% of organizations experienced a phishing attack in 2020, and the average cost of a phishing attack was $1.6 million. These statistics highlight the importance of education and awareness when it comes to social engineering and phishing attacks.
Adversaries Look For Sensitive Information in the Dark Web
In addition to social engineering and OSINT collection, adversaries often look to the dark web for sensitive information. The dark web is a clandestine network of websites and online marketplaces that operate outside the confines of the traditional internet. Here, adversaries can acquire sensitive information, including PII, financial data, and even strategic security clearances.
According to a report by the RAND Corporation, "The dark web is a growing source of sensitive information. Adversaries use dark web marketplaces to acquire sensitive information, including PII, financial data, and strategic security clearances."
Targeted Campaigns to Compromise Individual Security
Once adversaries have acquired sensitive information, they often use it to create targeted campaigns to compromise individual security. This can take many forms, including:
*
Password cracking, which involves using advanced algorithms to crack passwords and gain access to secure systems.
Malware deployment, which involves infecting systems with malware to gain access to sensitive information or disrupt critical infrastructure.
Ransomware attacks, which involve using malware to encrypt sensitive information and demand ransom in exchange for its safe return.
According to the FBI, ransomware attacks have become a significant threat to national security. In 2020, the FBI reported over 3,500 ransomware attacks, with losses totaling over $100 million.
Mitigating the Risk of Intelligence Gathering by Adversaries
While the threat of intelligence gathering by adversaries is real and growing, there are steps that can be taken to mitigate this risk. These include:
*
Education and awareness: educating individuals and organizations about the risks of social engineering and phishing attacks.
Implementing robust security protocols: implementing robust security protocols, including multi-factor authentication, encryption, and penetration testing.
Monitoring and incident response: continuously monitoring for potential security threats and having a robust incident response plan in place.
According to a former NSA cyber intelligence official, "Education and awareness are key to mitigating the risk of intelligence gathering by adversaries. By educating individuals and organizations about the risks of social engineering and phishing attacks, we can significantly reduce the likelihood of a successful attack."
In conclusion, the threat of intelligence gathering by adversaries is a real and growing threat in the digital age. By understanding what adversaries look for when gathering intelligence, we can take steps to mitigate this risk and protect our national security and individual privacy.



Related Post
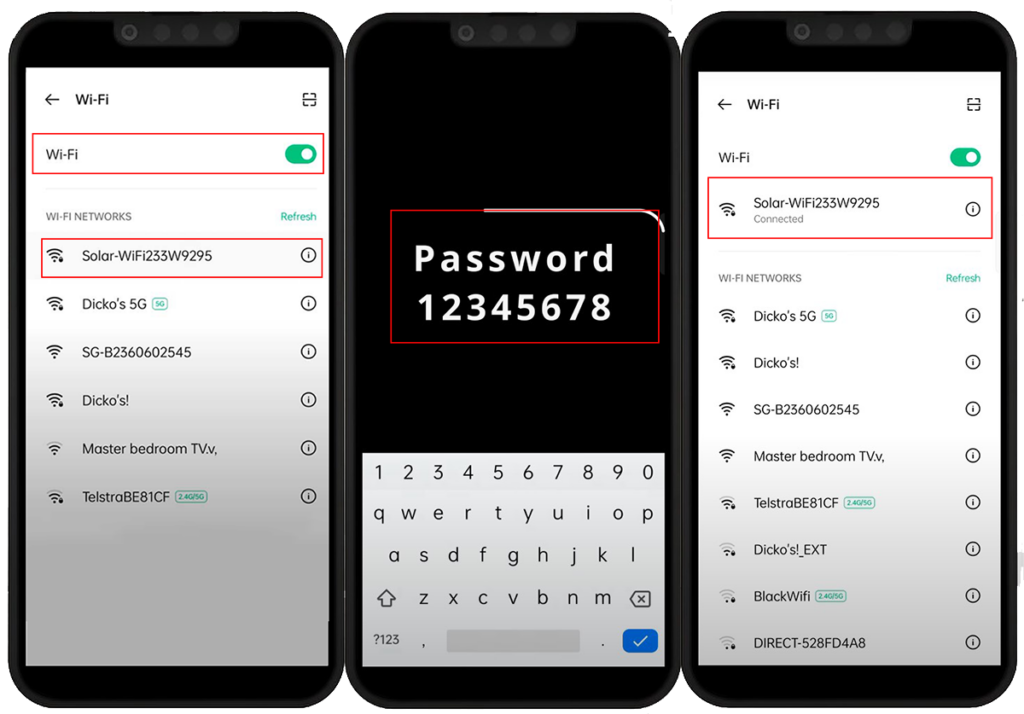
Unlock the Power of Your GoodWe GW3600D-NS with a Hassle-Free WiFi Setup

Michigan State Bar Member Directory: Unlocking Access to a Wealth of Legal Professionals
Unlocking the Past: Uncovering Local History through Winkel Funeral Home Obituaries
Anderson Cooper Husband: A Look into the Personal Life of the Renowned Journalist

